A complete caller info search for the numbers 3761751472, 3761752716, 3761763181, 3762230127, 3770812215, and 3773391458 reveals essential insights into their origins and potential legitimacy. Analyzing these specific phone numbers through various tools can uncover patterns, assess spam risks, and enhance personal security. The findings can inform users about their unknown callers, leading to more secure communication practices. However, the implications of these results warrant further exploration.
Understanding Caller Identification
How does caller identification function in modern telecommunications?
Caller ID technology utilizes a signaling system to transmit the caller’s number and name to the recipient’s device.
This process raises privacy concerns, as personal information can be easily accessed or misused.
Balancing the benefits of caller identification with the need for individual privacy remains a critical challenge in an increasingly interconnected digital landscape.
Importance of Caller Info Searches
Caller info searches play a critical role in identifying unknown callers, which can significantly mitigate the risks associated with unsolicited or potentially harmful communications.
By providing detailed information about the caller, these searches enhance personal security and empower individuals to make informed decisions regarding their interactions.
Consequently, the ability to ascertain caller identity fosters a safer communication environment in an increasingly connected world.
Identify Unknown Callers
Why might individuals prioritize identifying unknown callers in today’s communication landscape? As concerns over phone privacy escalate, understanding caller identities becomes crucial.
Effective caller etiquette dictates that individuals should discern legitimate contacts from potential intruders. By utilizing caller info searches, one can reclaim autonomy over communication, ensuring that engagements are meaningful and respectful, while safeguarding personal information from unsolicited or harmful outreach.
Enhance Personal Security
Utilizing caller info searches significantly bolsters personal security in an era marked by increasing telecommunication threats.
By identifying unknown callers, individuals can implement effective privacy measures that enhance personal safety. This proactive approach enables users to discern legitimate contacts from potential fraudsters, thereby minimizing risks associated with unsolicited communications.
Consequently, caller info searches serve as a vital tool in safeguarding one’s autonomy and personal information.
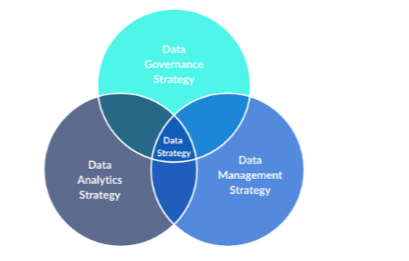
Analyzing Specific Phone Numbers
Analyzing specific phone numbers involves a systematic approach to verify caller identity and assess potential spam indicators.
This process incorporates examination of location data, which can provide insights into the legitimacy of the call.
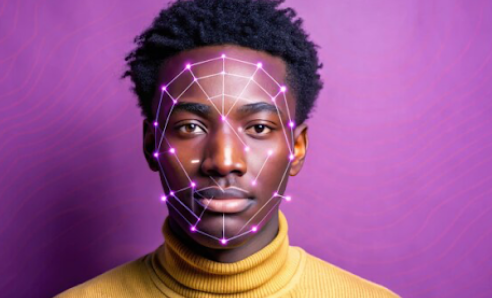
Caller Identity Verification
How can one ensure the authenticity of a caller’s identity? Employing robust caller verification methods, such as cross-referencing caller ID with reputable databases, is essential.
These methods not only enhance security but also address privacy concerns by limiting unauthorized access to personal information.
Understanding these verification techniques empowers individuals to safeguard their communications while exercising their right to privacy in an increasingly connected world.
Potential Spam Indicators
Identifying potential spam indicators requires a systematic examination of specific phone numbers that frequently appear in unsolicited communications. Analysts observe spam call patterns, noting repetitive dialing frequencies and call times.
Additionally, suspicious number characteristics, such as unusual area codes or non-standard formats, can signify fraudulent intent. Comprehensive analysis of these factors provides insight into the likelihood of a number being associated with spam activities.
Location Analysis Insights
While the geographic origin of a phone number can provide valuable context, it is essential to evaluate the implications of its location in spam detection.
Location tracking can reveal geographical patterns indicative of spam activity. Analyzing these patterns aids in identifying potential threats, enabling users to make informed decisions about incoming calls.
Understanding the relationship between location and spam enhances overall communication security.
Tools and Resources for Caller Info Searches
As the need for accurate caller information continues to rise, various tools and resources have emerged to facilitate this process.
Caller search tools, including comprehensive databases and reverse phone lookup services, enable users to access detailed caller profiles.
Online resources, such as community forums and mobile applications, further enhance the search experience, providing real-time updates and user-generated insights into unknown callers.
How to Protect Yourself From Spam Calls
A significant number of individuals face the persistent challenge of managing spam calls, which can disrupt daily life and compromise privacy.
Effective spam call prevention involves utilizing caller block techniques, such as enabling features on smartphones that filter unwanted numbers.
Additionally, registering with national do-not-call lists can further enhance protection.
Employing these strategies empowers individuals to reclaim their communication space and maintain personal security.
Reconnecting With Unknown Numbers
Spam call prevention measures can sometimes lead to missed opportunities for reconnection with unknown numbers, particularly from legitimate contacts.
Employing reconnecting strategies, such as using reverse lookup services or social media inquiries, can facilitate identification of unknown contacts.
This analytical approach not only enhances communication potential but also safeguards personal freedom, allowing individuals to discern valuable connections amidst a landscape cluttered with unsolicited calls.
Conclusion
In the intricate web of communication, each phone number serves as a thread, weaving together tales of identity and intent. By unraveling the mysteries behind numbers such as 3761751472 and 3773391458, individuals can illuminate the shadows where spam lurks and clarity prevails. Armed with the right tools and knowledge, one can navigate this labyrinth with confidence, transforming uncertainty into informed action, and ensuring each call resonates with purpose rather than dissonance.